It was early December 2016. The period of the year when it showers in Tbilisi and prepares you for winter. The day was not an exception either. I got a call from my ex-partner, who asked me to come outside to talk. He was waiting in front of my house in the street.
Our separation was very recent: My heart still sped up when I saw him, and I could still feel the tension between us. I wondered what else he had to say to me, after telling me he still loved me even though he wanted to be with someone else.
As I soon found out, life is full of invasions, and this meeting was no exception. He told me he knew the password of all my social website accounts and email—and had direct access to all my electronic devices. As proof, he mentioned a few things that he could only know if he had really hacked me. He told me if I did not stop writing the story I was working on, he and “other people” would destroy me.
That day became a turning point in my relationship with the world wide web.
Instead of coming up with more complicated passwords for my social media accounts, I gave up and stopped taking any security measurements. I stopped writing whatever I was writing.
I also stopped believing in the utopian dream that the internet would give us total freedom and democracy, create a place where everyone is equal and the security of personal information is the number one priority.
A few years later, a new friend asked me if I had ever heard of the dark web. I was familiar with the deep web, the encrypted part of the internet that requires users to know special passwords to gain access to websites. But the dark web was new to me.
We were sitting in a loud bar, drinking chacha (Georgian grappa) and I recall trying to catch a bit of hope in his words, a glimmer of possibility that the Internet may yet offer the level of security I thought I lost.
He explained the dark web as the concept of secured Internet browsing, a version of the Internet where you can do anything and still stay anonymous. Access is simple: download a TOR browser and away you go.
But nothing is really that simple, especially when discussing the dark web. For starters, the only thing TOR does is change your IP to a random address from somewhere else in the world.
Second, of course, is that the dark web is much more than secure browsing. Created to allow sensitive agencies, like defense ministries, to use the Internet without leaving a footprint, it has evolved into a chaotic marketplace, where illegal activities flourish. In Georgia, for example, the dark web is mostly popular for buying drugs, selling the personal data of people who use Georgia’s online casinos and journalism.
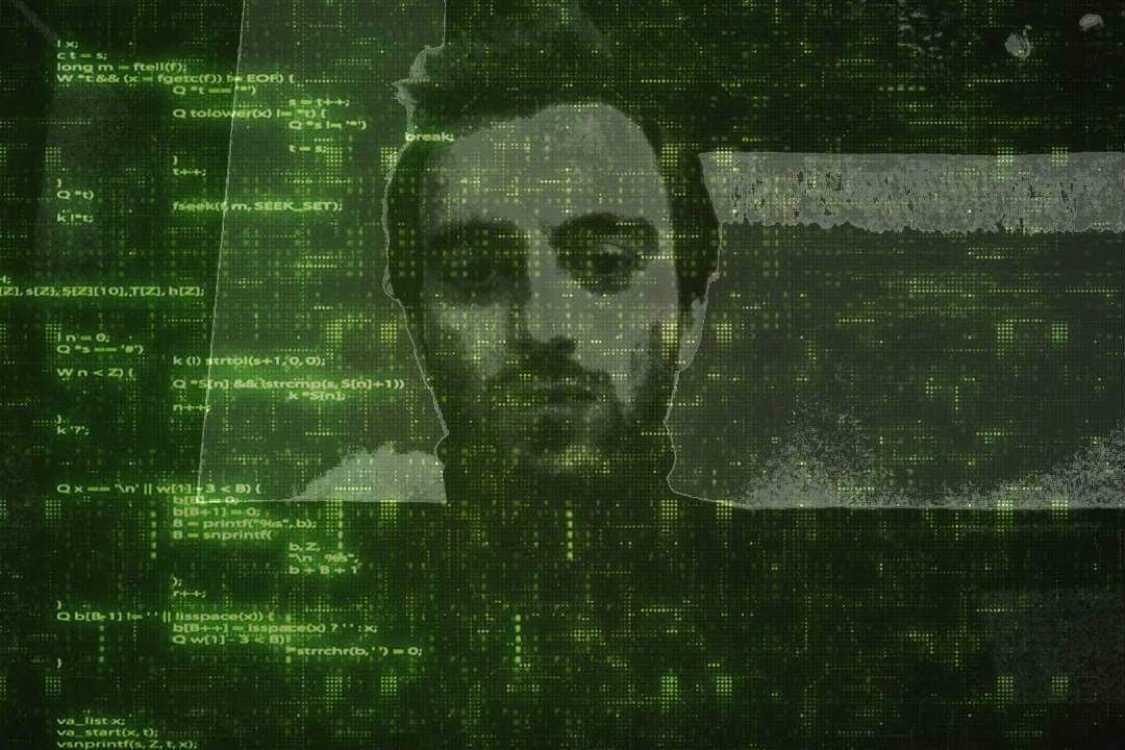
My friend, who told me about the dark web--we will call him Deniz Aksoys to protect his identity—grew up along with the technology that enabled the dark web, in addition to the apps we trust with all our personal data.
He was just 12 when his father got one of the first personal computers. It was the 1980s, in post-coup Istanbul. The family owned an electronics shop and, one day, instead of the usual cassette players, a delivery guy dropped off a box from the UK.
Deniz recalls the drop off—the delivery guy treated the box like it was a package of kebabs. But his father was nervous, admonishing Deniz to be careful as he opened it. Inside, nestled in foreign packaging, was the Spectrum ZX 81, one of the first personal computers produced by the British Sinclair Research firm.
The computer connected straight to your television rather than a monitor. The programs and the data were loaded on compact audio cassettes. Its memory was one kilobyte. For reference, the smartphone you are using to read this story holds at least 120 million kilobytes.
But for Deniz, it was a kilobyte of pure wonder. He quickly mastered the technology, moving from programming to hacking as he grew from a child to a teenager. There was a time, he recalls, when hackers had to take over an entire computer system to create a tiny image on the screen.
“Those guys were the real software hackers. Hacking through the computer's graphic processor and pushing it to the limits. We burned a lot of graphics cards while experimenting, because that’s not really easy to do. And that was the time when the speed of the internet was 9600 bauds per second. Now my phone connects four million times faster,” he says.

After the Turkish Ministry of Education started to invest in new computing systems and technology, Deniz moved his extracurricular internet “research” to his high school classroom.
“When I started studying at the university for mathematics and computers, I was already on my third [IT] job. But I was lucky. No one knew anything about the new technology, and I was simply too curious, reading all the manuals and boring books” Deniz recalls.
By the age of 25, he was already working as an IT consultant for the Turkish government, helping the health ministry create a single online network. He remembers that his monthly salary was enough to buy two beers and cover his daily bus fare.
But outside of work, Deniz was immersing himself in the works of the pioneers of technology. He read American writers Alvin Toffler and John Braner, who wrote about how new technology was changing the human psyche. Toffler saw technology advances as a series of “waves.” He believed the 20th century, especially WWI and WWII, created the shocks that eventually led to the computer and the Internet. Deniz was particularly enthralled with Toffler’s prediction of a third wave—the coming of the digital age.
He saw himself in John Braner’s 1975 Shockwave Rider.
“There was nothing called a hacker back then…Back in the 70s, this author described what’s happening today in the world, where it is very hard to hide already having our digital footprint everywhere,” Deniz says.
Writers were not the only ones who worried about the accessibility of technology and its power. Around the same time that Toffler and Braner were imagining the power of the future internet and its impact on humanity, governments were investing in a special type of internet, known colloquially as the dark web, which would be closed off from the general public. Access would be limited but, once inside, everything would be untraceable.
Initially, people needed special software to access the dark web, Deniz explains. But by the early 2000s, the U.S. Naval research lab created one of the first--and the still the most popular--dark web browser, TOR.
It was created for the intelligence officers to use the internet anywhere without being tracked. But by 2004, the TOR browser became accessible to everyone, everywhere.
Over the past 15 years, people have used the dark web to plan and spread information about the Arab Springs and other revolutions in oppressive regimes. Journalists and other people have used to uncover government secrets, like WikiLeaks. Today, major news organizations host versions of their websites on TOR browsers, to ensure they are accessible even to people in countries where media sites are largely blocked.
Deniz, for example, uses TOR and the dark web to buy bitcoin and find information for investigative journalists working in Georgia.
But he cautions that TOR and the dark web are far from the utopia he and others dreamed of back in the pioneering days of the world wide web.
“Dark web is not anarchy. It is organized crime. If you define anarchy as not being under any kind of authority, the dark web is already under some kind of authority,” he says, noting that the very internet we all depend on every day is based on the technology developed for the US Defense Department’s Advanced Research Projects Agency Network.
“When I started doing this, it [hacking] was all about anarchy, giving free information to the general public, journalist researchers. Now it is more about money. This is not the true idea of being a hacker. A hacker has become a guy in a hoodie trying to take your mom’s savings. That’s criminal. That’s not a hacker,” he says, stressing that he never wears hoodies.
Every coin has two sides, as the saying goes. In the case of the dark web, on one side, it can be used for criminal pursuits. But on the other side, it can also be a tool to fight for utopian democracy. But don’t forget: on the dark web, the market is run by cryptocurrency—bitcoin—which is more like an onion than a coin, hiding layers upon layers.
“My anarchy is this: never give up and never stop trying,” Deniz says. He added that curating our own digital profile will be critical to preserve our identities.
DONATE NOW


